We are back once again for another monthly round up for Celo network.
Target APY
In our previous issue we discussed how Rewards Multiplier affects Target APY.
Downward trend continues for Rewards Multiplier thus Target APY continues to decrease.

Target APY for July, 2020
Digging deeper in CELO economics
It would be natural to wonder if the downward trend for Target APY is worrisome or not, or how bad would it be if
Target APY were to drop as low as 5% instead of the target 6% for example?
DISCLAIMER Thoughts below are my opinions only and should not be taken as an investment advice in any way. Also, I am not an economist, which makes these opinions even less scientific.
As discussed in previous round-up, downward trend in Rewards Multiplier is consequence of more than the target amount
of CELO being locked for staking in the network. While this causes reduction in Validator and Voter Rewards, there is a natural
counter balancing element to it. If more CELO is locked up in steady state, that should lead to decrease in liquid supply,
which should lead to higher prices for CELO on the exchanges. Thus, in theory, if Target APY is decreasing, there is a good
chance that CELO’s price compared to other assets should be increasing due to reduced supply, which should encourage all
CELO holders to sell some small percentage of their holdings, bringing liquid supply back to target levels and bringing
Rewards Multiplier back close to value of 1.0 too.
Balancing mechanisms in CELO
Celo protocol overall has many such balancing mechanisms. These mechanisms seem to be devised to allow for sustainable and more stable growth rather than very volatile huge price swings. This is definitely different compared to a lot of other crypto protocols where unintentionally (or maybe sometimes intentionally) high volatility is not only the norm but also the desired behavior.
Examples of mechanisms in Celo that keep counter balance to large price increases for CELO token:
- Reserve:
- Since reserve is balanced using basket of crypto currencies, it provides counter acting downward pressure when price of CELO increases by a lot.
- Downward pressure of reserve rebalancing is even more pronounced while there is still close to 18 months left until most of it becomes unfrozen.
- Dynamically adjusted
Rewards Multiplierbased on locked vs liquid CELO tokens as explained above.
Examples of mechanisms that counter balance large price decreases for CELO token:
- Validator EpochRewards: Since validator rewards are payed out in cUSD, it gives CELO token a baseline value compared to US dollar. If CELO price were to drop against USD significantly, there would be natural counter balance to buy up more CELO to run more validators to earn more cUSD rewards.
- Reserve: Similarly as described above, rebalancing process of the reserve can also provide demand for CELO when its price drops significantly against other assets.
Another interesting aspect of Celo protocol is that it seems to provide very clear mechanisms to tie its value more closely to its usefulness. Celo’s objective usefulness can be tied to overall demand for cUSD and other future cXXX stable tokens that get issued on the network. Due to how reserve and other mechanisms are setup, high demand for cUSD should lead to larger reserve, which should lead to reduced liquid supply for CELO, hence higher prices for it. Similarly, low demand or decreasing demand for cUSD and cXXX tokens should lead to smaller reserve, hence more liquid CELO supply and lower prices for it overall.
These thoughts are one of the main reasons why we are excited about Celo overall. Protocol and its economics makes a lot of sense from first principals perspective. Instead of depending on wild speculation or unsustainable growth schemes, Celo network provides a very clear path for growth as long as it actually becomes useful to people.
Of course, all of this is in theory. Real world rarely tends to be too rational. While mechanisms make sense, the parameters that govern those mechanisms can still have unintended or unexpected consequences. Only time will show what comes out of this all as years go by.
Network security and stability
After all this armchair economics breakdowns, lets get back into our actual area of expertise and provide some round up on validator performances for the last month.
Emergency client upgrade due to Security vulnerability
In July, first serious security bug was found in Celo client, which prompted an emergency patch and a necessary timely upgrade of all validators to the patched version.
Naturally, first such event caused a bit of a mess for some validators, but nothing too major. Network still remained operational and security issue was discovered, fixed and deployed before anyone attempted to exploit it.
Three groups: TDLabs,
Manta Labs, and
Bison Trails suffered largest outages.
TDLabs and Manta Labs groups crossed slashing thresholds too but since slashing is still not enabled on the network,
no actual slashing took place.
At least 5-6 other Groups had significant outages too (>10 minutes) during the upgrade, but not on the same scale as the above three.
While having a large outage is never great, we want to call out Bison Trails group that handled their outage in much more responsible
way compared to others, at least in our opinion. They were very active and responsive in the Discord channel. They worked with the cLabs
team to find a solution for their tricky problem. Got a patched fix from the cLabs team and deployed it to bring back their validator
before it would cross the slashing threshold. In addition to all that, they also produced a public
incident report.
Evaluating emergency upgrade response
While immediate issue is fixed, this process is still not over until minimum client version gets upgraded. Governance proposal for it will most likely get delayed since its safety is still questionable right now.
If we were to score response to this first serious issue, we would rate it as B-. Pretty good, but can definitely be improved.
Things that went well:
- Issue was discovered and patch was distributed to most critical parties involved fairly quickly without public announcement.
- Once announced publicly, validator upgrades that closed off immediate exploit were deployed pretty quickly (within ~2-3 days).
Things that didn’t go so well:
- Non trivial amount of validators had significant outages due to the upgrade.
- Many validators opted to upgrade Proxy only without upgrading the Validator due to extra complexities.
- Finalizing “minimum version” update will be delayed significantly since there is no easy way to tell what version of client software is run by different validators. This keeps exploit “live” for users who might still be running affected version of client software.
Validator Group performance
To wrap things up, we provide Validator Group performance stats once again for month of July too. If you need a refresher on how
validator uptime affects estimated APY check out Uptime Overview section from our first round up.
Once again we list all the Estimated APY stats here from last months performance, using https://celovote.com/scores?lookback=31
as a source. You can always check Estimated APY based on longer performance history at https://celovote.com/scores.
As in pervious months, the large majority of the groups have had close to perfect uptime this month too.
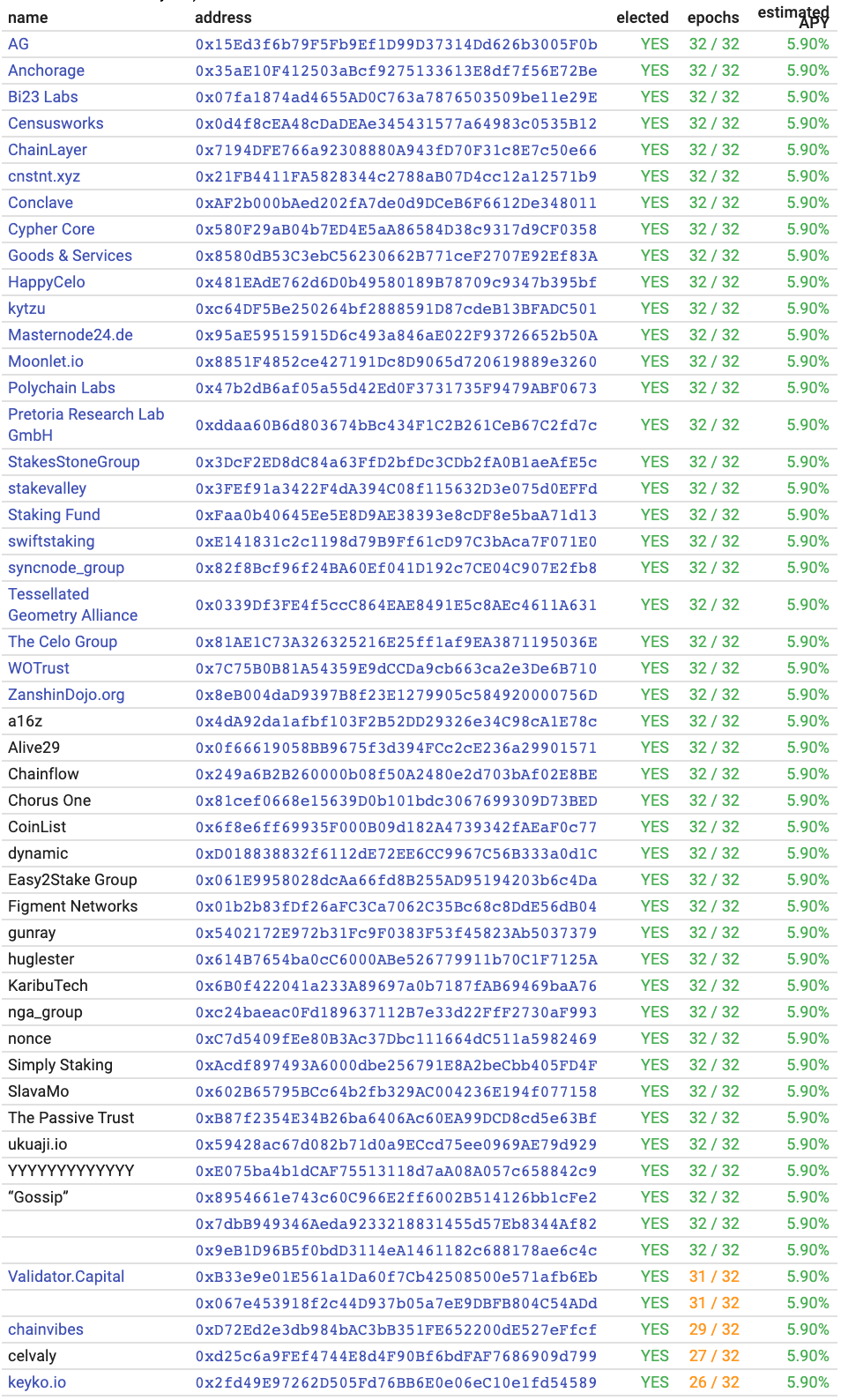
Snapshot of Estimated APYs from https://celovote.com/scores
Small subset with minor issues.
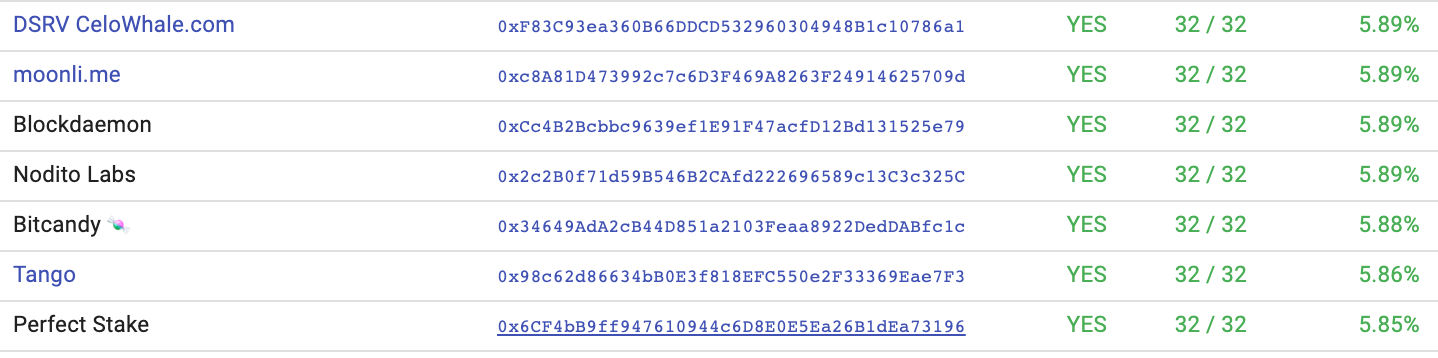
Snapshot of Estimated APYs from https://celovote.com/scores
And even smaller subset have had larger issues.
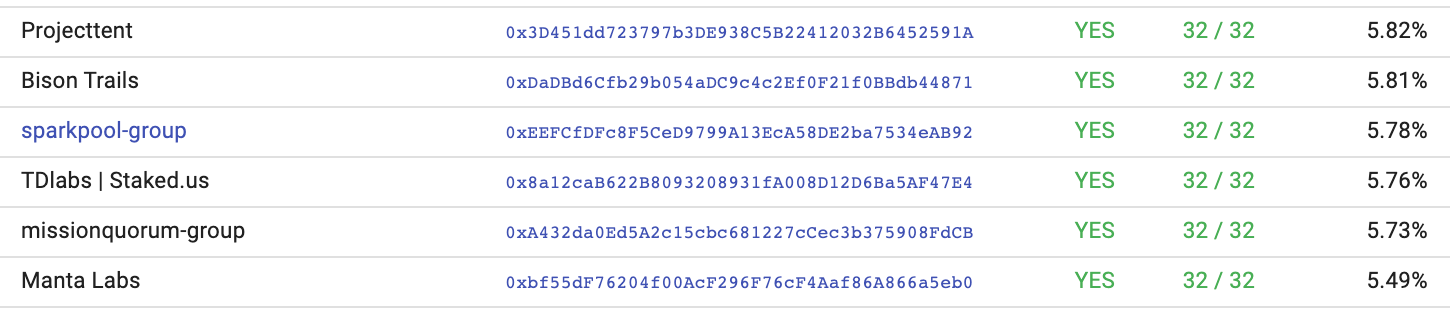
Snapshot of Estimated APYs from https://celovote.com/scores
There seems to be an interesting trend that total number of groups that have larger issues remains mostly same from month to month, however there are much fewer “repeated offenders” (i.e. groups that have larger issues in subsequent months). This makes sense since operational issues can be random and sometimes luck dependent, thus it makes sense that we should use as much past data as possible to predict future performance. Currently Celovote scores can only look back up to 90 epochs for past performance, but we are working on making it more efficient to look back as far as 180 epochs, and ideally even as far as 365 epochs to cover the full year.
Wrap up
This was certainly most eventful month operationally since launch of the Celo network. However, we are still in very early days of operations. Valora wallet is still not launched, thus there is still very minimal amount of traffic that network has to serve. Real test of the network is will start once there is actual real usage and traffic on it. On the other hand more real validation of Celo economics will start to happen once cUSD gets listed directly on the exchanges.
Exciting times are ahead.